This post explains about how an Azure account is managed, what are the different administrative roles , what they do in managing Azure subscriptions, and how Azure Active Directory (AAD) is connected in managing Azure accounts and subscriptions.
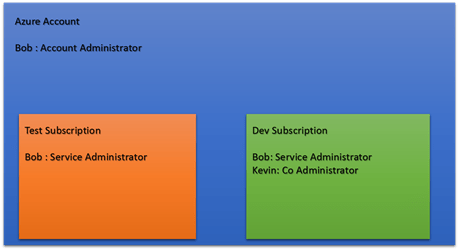
An Azure account is simply a container for managing subscriptions. All the services we use in Azure are contained in a subscription. One Azure account can have multiple subscriptions. Consider the below scenario to understand the concept.
I have marked few important rules, which I consider the rule of thumbs to remember in Azure account administration.
Azure Account
There are several ways that you can get access to Azure, you can start a free trial, you might get Azure credits from any of the enterprise licenses your company has with Microsoft or through any other non-documented or unclarified methods.
But let’s begin the story in a more simpler and practical way. Assume Bob wants to learn Azure and wanted to buy an Azure account. Bob entered his credit card detail and activated the Azure account, during this registration process Bob entered his personal email address bob@outlook.com.
- Bob got an Azure Account.
- Bob created a subscription in order to access Azure services since Azure account is a container for the subscriptions.
- Bob named this subscription Dev Subscription.
- One Azure account can have multiple subscriptions and each subscription can have different payment options as well.
- Since Bob owns the Azure Account he becomes the Service Administrator for the Dev Subscription and also he is the Account Administrator.
- Later Bob created another subscription for testing and he named it Test Subscription.
- Bob is the Service Administrator for both subscriptions.
- Then Bob added Kevin as a Co Administrator in the Dev Subscription using Kevin’s email address kevin@outlook.com.
After the above steps, this is the logical structure of the Bob’s Azure account.
Account Administrator: Account Administrator is the person who owns the Azure account, he is the only person who can manage subscriptions (create, edit, change payment plans).
Service Administrator: Service Administrator has full privileges inside the subscription. One subscription can have only one service admin. He has full rights in managing all the resources and services inside the subscription including adding / removing Co Administrators.
Co Administrator: Co Administrators have full rights in managing resources and services inside a subscription, except they cannot manage users, meaning they cannot manage other Co admins or Service admins.
Read this link for detailed information about the above administrator roles.
Rule #1
- In order to login to Azure, a user should be either a Service Administrator or a Co Administrator of the subscription.
As you see Kevin is a Co Admin in the Dev Subscription and he has full rights in managing the resources in the Dev Subscription. But he doesn’t see the Test Subscription. Kevin can be an Account Administrator / Service Administrator of some other Azure Account with the same email address. In that case when he logs into the Azure Portal he will see all the subscriptions in the drop down. He can select the subscription he wants to work with. Any programmatic operation requires the subscription Id.
Azure Active Directory and Azure Account Management
Azure Active Directory (AAD) plays a major role in the Azure account management. Even in the scenario explained above, it has a big part though the process is totally transparent. This is where I put the second rule in.
Rule #2
-
In order to authenticate to Azure you need Azure Active Directory authentication, in the other terms Azure only trusts the Azure Active Directory authentications.
In the above example Bob and Kevin has no knowledge about AAD, they simply added their personal Microsoft email addresses and everything works.
Bob or Kevin logs into Azure portal using their personal Microsoft email addresses (bob@outlook.com / kevin@outlook.com). Technically they use the Microsoft email authentication to access Azure. This is a huge contradiction to the rule #2.
Answer is very simple, in order to make sure the customer experience smooth and non-cumbersome Microsoft has taken efforts that Azure Active Directory trusts the Microsoft consumer authentication tokens.
So when Bob / Kevin is authenticated via their consumer authentication credentials, the token is passed to the AAD, which trusts the consumer identity token and authenticates them to the Azure portal.
Azure automatically adds Service administrators and Co Administrators to the Azure Active Directory associated with the subscription.
Consider the below cases for the detailed clarification.
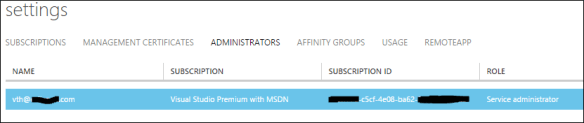
Service Administrator is a member and the Global Administrator of AAD
There’s a Service Administrator and he’s a member of AAD as well. The first image shows the Administrators section of the settings page and the second image shows the AAD users section. Azure has added the Service Administrator automatically in the AAD as a user, typically with the Global Administrator permission for the AAD.

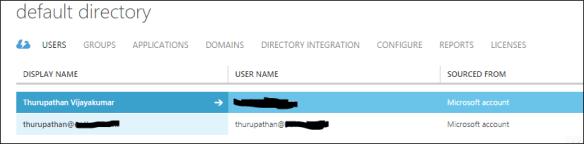
Co Administrators are automatically added to the AAD with user roles
Now I want to add a Co Administrator to this subscription. When you click the Add button in the portal you will get a window with this message on top.
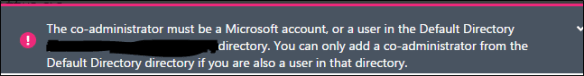
As you see the message is very clear. It is the combination of rule #1 and 2.
When you add a user with Microsoft account and add him / her as Co Administrator he / she will automatically be added to the AAD users. The first image shows the Administrators sections of the settings page and the second image shows the AAD users section.

AAD can have the following sources.
- Microsoft Account
- Azure Active Directory Account
- Local Active Directory Account – when a local AD is synced with AAD
We were unable to find any subscriptions associated with your account.
The above is a very common message people get with the image below.
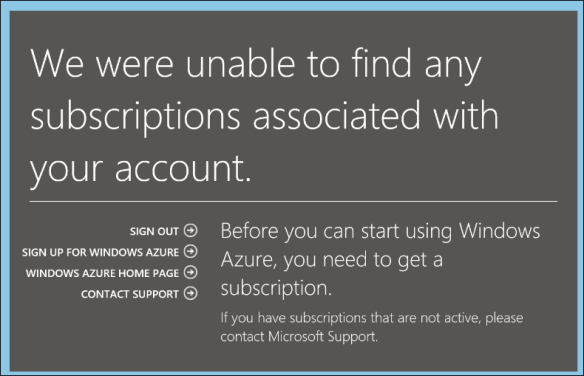
The reason is when you add a Co Administrator the user is added to the AAD, but when you remove a Co Administrator the user in the AAD remains undeleted. Because the user might have some other apps he/she has been accessing using AAD credentials.
In this case if the user tries to access the Azure portal they will get this message. Because here the rule #2 is true but rule #1 is false.
Azure Account Management Best Practices
It is highly recommended not to use Microsoft consumer identities especially the root accounts to access the Azure portal for the day to day tasks. In our case study bob@outlook.com is the root account. Always create a AAD users with specific roles and use them for development purposes.
